How to get more leads, sales, and income.

One of the pitfalls of being a business coach is that the best coaches often have no problem helping their clients grow their businesses, but can’t seem to grow their own business the way they want to. If you fall under this umbrella, know that it is not your fault!
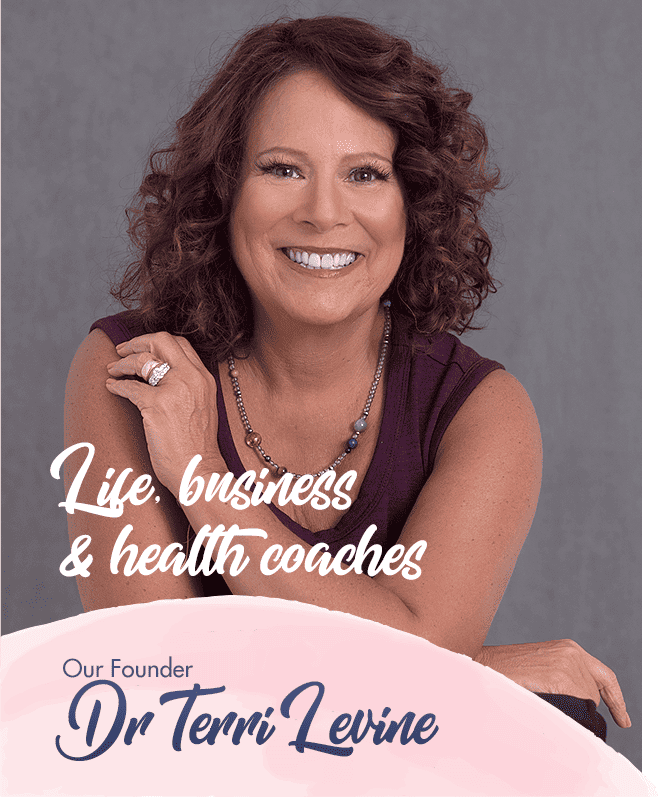
Being a business coach is wholly unlike running any other type of business. As a business coach herself, our founder Terri Levine has helped hundreds of coaches add hundreds of thousands in revenue with our business coach marketing and mentorship program.

Whether you are an established life coach, or just wondering how to become a life coach, our program may be a great fit for you. Our founder, Terri Levine, a “life coach business coach” has helped thousands of coaches generate 6 and 7 figure incomes, while taking a people centric approach to their business and truly serving their clients needs.
If you are looking to accelerate your business growth, learn how to market a life coaching business, and generate a life coach marketing plan resulting in revenue growth of over $100,000 in the next 6 months, we can help.

Helping people to reach their health goals can be a very satisfying career. Our founder Terri Levine, has been assisting with marketing for health coaches for over 20 years. She has helped hundreds of health coaches reach their financial goals, often tripling or even quadrupling their income, while taking a client focused approach to their business!
If you are wondering how to market your health coaching business and looking to dramatically grow your revenues while providing excellent service to your clients, we can help.


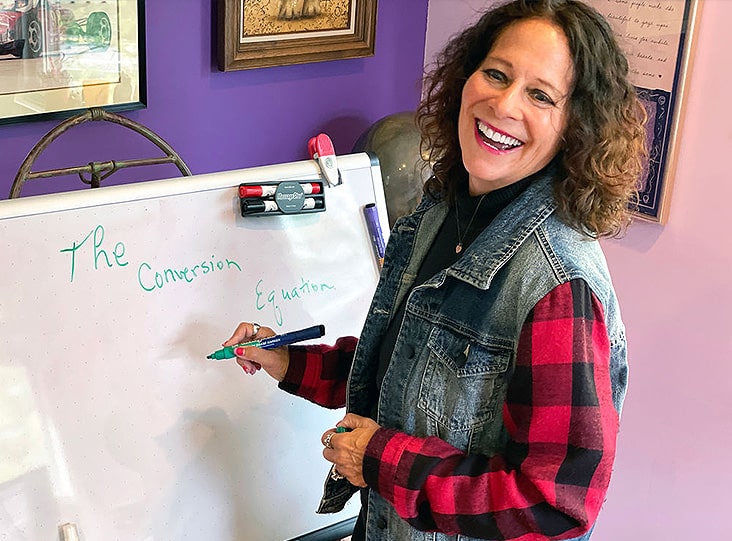
I will show you how I made an Extra $64,238 last month just using social media organically- no ads – and how you can do this!
This was achieved by leveraging the power of my personal brand and by using my online coaching/consulting business model and I will show you how you can do this, also.
We offer life coach marketing plans, business coach marketing, marketing for health coaches, strategy sessions with our founder, Dr. Terri Levine, and much, much more.
Our strategies have a 100% success rate for all who implement them. If you need a marketing plan for your life coaching business, business coaching practice or health coaching business, or need advice on how to acquire and retain more clients, contact us today!








Known as the business mentoring expert with heart, Terri is one of the world’s top business and marketing strategists. Terri is known for consulting with business owners to help them move from ineffective traditional sales, marketing and operational methods into effective, authentic and transparent people centered communication models.
Terri has over 43 years of business, sales and marketing experience, and has helped over 7,200 business owners reach revenue goals they never thought possible. She is one of the world’s foremost experts on how to market a coaching business. She has built and sold several multi-million dollar companies. She is a best-selling author of over 40 books, and a highly requested keynote speaker at events and conventions throughout the world.

Get access to a 5-day email course with a simple, actionable framework to use to start building a massive and engaged audience, TODAY.


Know how to get more leads, sales, and income from your coaching business.
Heart-repreneur® LLC© 2024 Privacy Policy